Across the UAE, a dangerous assumption persists that a clean Vulnerability Assessment and Penetration Testing (VAPT) report means an organization is secure. This belief is not just misguided it is a direct path to regulatory failure and data breach.
This scenario plays out hundreds of times each year across the UAE’s enterprise landscape. And it reveals a dangerous misconception: that a periodic VAPT assessment is equivalent to a mature information security program.
It is not.
For enterprise organizations in the UAE, particularly those regulated by the Telecommunications and Digital Government Regulatory Authority (TDRA) or the Dubai Electronic Security Center (DESC), relying on VAPT alone is insufficient. The UAE government’s Information Assurance Framework (IAF) makes this clear: security requires continuous governance, not point-in-time testing.
The VAPT Trap: What It Misses
Vulnerability Assessment and Penetration Testing are valuable tools for identifying technical flaws. However, they have fundamental limitations:
Consider this scenario: An enterprise passes its annual VAPT. Three months later, a former employee whose access was never revoked exfiltrates customer data. The VAPT never tested the offboarding policy. The breach costs millions. The VAPT offered no protection.
The Enterprise Reality: Why Continuous Review Is Essential
Enterprises in the UAE face threats that VAPT alone cannot address. These include:
- Dynamic Threat Landscapes: Cyber threats evolve daily. A vulnerability that was unknown during your last VAPT may be exploited next week. Zero-day exploits, ransomware variants, and supply chain attacks emerge constantly. Only continuous monitoring and control review can keep pace.
- Regulatory and Contractual Obligations: Organizations operating in the UAE’s financial, healthcare, energy, or government sectors face stringent compliance requirements. The Central Bank of the UAE, the Securities and Commodities Authority, the Dubai Financial Services Authority (DFSA), and the Dubai Electronic Security Center (DESC) all mandate ongoing security governance, not just annual testing.
- Insider Threats: According to multiple industry reports, insider threats, whether malicious or accidental, account for a significant percentage of data breaches. VAPT cannot detect whether an employee has installed unauthorized software, bypassed data loss prevention rules, or shared sensitive information externally.
- Third-Party and Supply Chain Risk: UAE enterprises increasingly rely on cloud providers, SaaS platforms, and external vendors. Each third party introduces risk. VAPT conducted on your internal systems says nothing about whether your payroll provider has been breached or your cloud storage bucket was misconfigured.
- Policy and Control Drift: Even well-designed security policies erode over time. Employees find workarounds. Managers approve exceptions. Legacy systems accumulate. Without continuous review, controls that were effective at deployment become ineffective through gradual, unnoticed drift.
The IAF Framework: The UAE Government's Blueprint
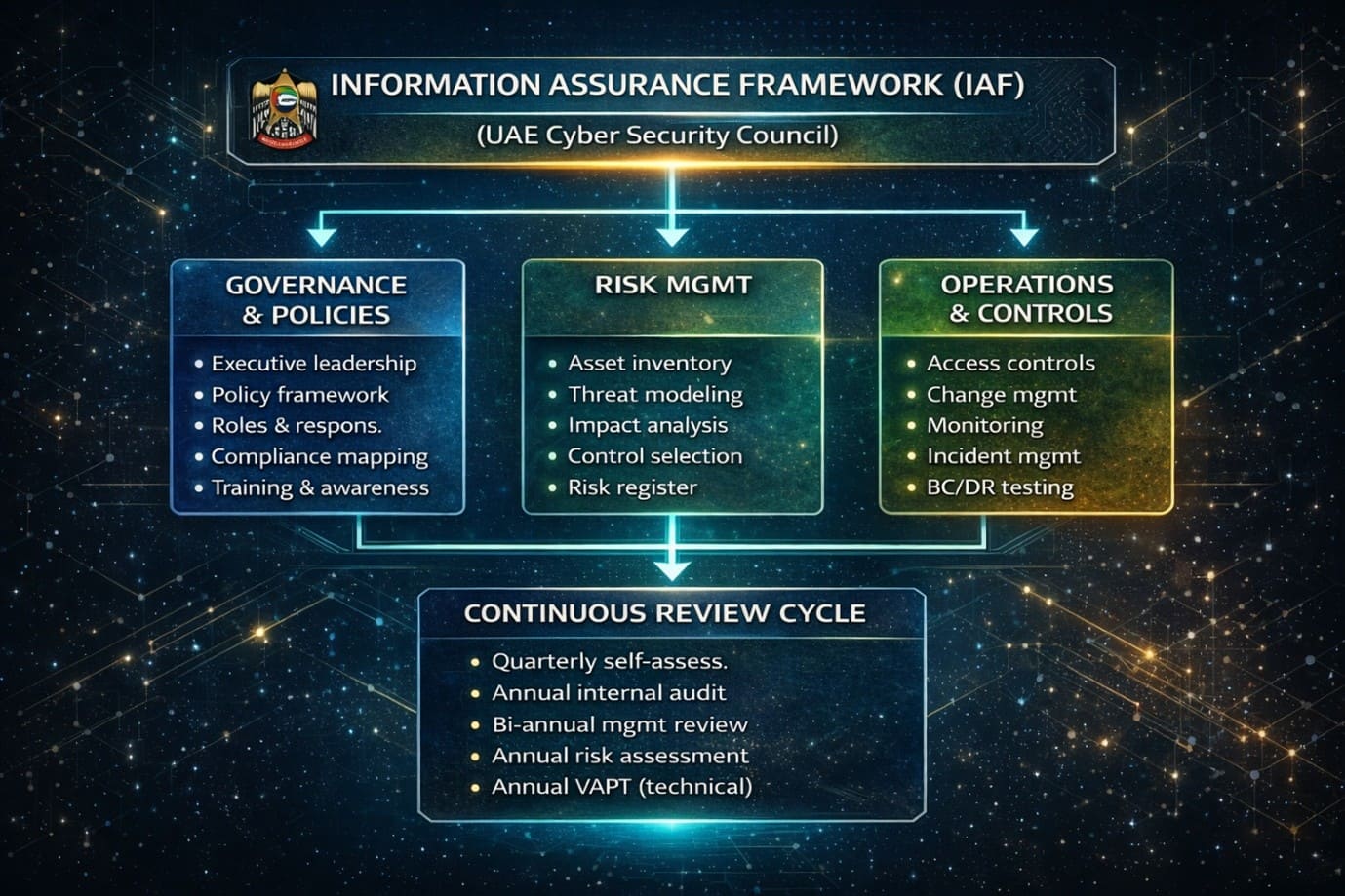
Recognizing these limitations, the UAE government has developed and mandated the Information Assurance Framework (IAF). The IAF is not a single document but a comprehensive approach to security governance overseen by the UAE Cyber Security Council and implemented by sector regulators, including TDRA, DESC, and ADDA.
The IAF is aligned with international standards, specifically ISO/IEC 27001:2022, while incorporating UAE-specific legal, regulatory, and national security requirements. It provides a structured, risk-based methodology for organizations to assess, implement, and continuously improve their information security posture.
Why the IAF Mandates More Than VAPT
The IAF explicitly requires organizations to implement a management system for information security, not merely technical testing. This management system encompasses:
- Governance and Leadership Commitment: The IAF requires executive-level accountability for information security, documented policies approved by management, and regular governance reviews.
- Risk Management Processes: Unlike VAPT’s technical focus, the IAF demands a systematic risk assessment methodology that considers business impact, threat likelihood, and control effectiveness across all domains—people, process, and technology.
- Continuous Monitoring and Review: The IAF establishes requirements for ongoing security monitoring, regular control testing, management reviews, and continuous improvement cycles.
- Policy Lifecycle Management: The framework requires that security policies be regularly reviewed, updated, communicated, and audited for compliance—not simply written once and filed away.
- Incident Response and Business Continuity: Organizations must have tested, documented plans for security incidents and disruptions, with regular exercises and reviews.
- Compliance and Assurance: The IAF demands evidence of compliance through internal audits, management reviews, and, where applicable, independent certification.
The Cost of Getting It Wrong
Enterprises relying exclusively on VAPT face regulatory penalties under the PDPL and DIFC Data Protection Law, operational disruption from ransomware attacks, reputational damage that erodes customer trust, and potential executive liability under UAE cybercrime laws.
Conclusion
The IAF recognizes what too many organizations discover only after a breach: security is not a test you pass once per year. It is a continuous discipline of governance, risk management, and control review.
VAPT has its place, but it is a tool, not a strategy. UAE enterprises must build IAF-aligned programs with continuous review cycles embedded into their operations. Document policies. Test controls quarterly. Review risks annually or upon any significant change. Conduct management oversight regularly and treat VAPT as one valuable input to a broader assurance framework.
The organizations that embrace this approach will achieve genuine resilience. Those that do not will learn the hard way that a VAPT report offers no protection against the threats they never tested for.
How MAST Consulting Can Help You Move Beyond VAPT
MAST Consulting helps UAE enterprises move beyond periodic VAPT to continuous, IAF-aligned security governance. We build and enhance ISO 27001-based ISMS frameworks, enable continuous risk and control monitoring, and strengthen compliance with TDRA, DESC, and UAE regulatory requirements.
We also support third-party risk management, incident readiness, and ongoing control assurance, ensuring security is not just tested once—but continuously managed.
With MAST Consulting, organizations achieve real, ongoing cyber resilience—not just a clean VAPT report.




